Funny how CrowdStrike already sounds like some malware’s name.
It literally sounds like a DDoS!
Botnet if you will
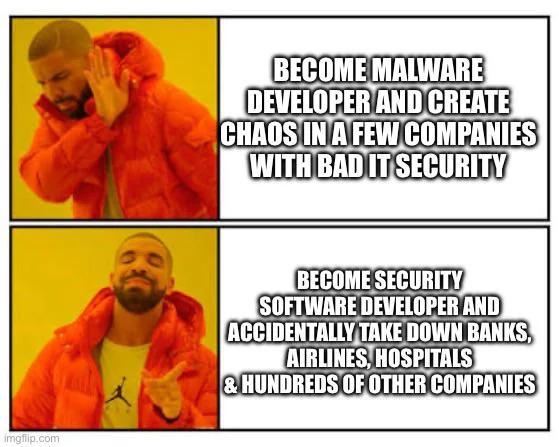
Not too surprising if the people making malware, and the people making the security software are basically the same people, just with slightly different business models.
Reminds me of the tyre store that spreads tacks on the road 100m away from their store in the oncoming lanes.
People get a flat, and oh what do you know! A tyre store! What a lucky coincidence.
Classic protection racket. "Those are some nice files you've got there. It'd be a shame if anything happened to them..."
This is, in a lot of ways, impressive. This is CrowdStrike going full "Hold my beer!" about people talking about what bad production deploy fuckups they made.
You know you’ve done something special when you take down somebody else’s production system.
*production systems around whole world
I'm volunteering to hold their beer.
Everyone remember to sue the services not able to provide their respective service. Teach them to take better care of their IT landscape.
Typically auto-applying updates to your security software is considered a good IT practice.
Ideally you'd like, stagger the updates and cancel the rollout when things stopped coming back online, but who actually does it completely correctly?
Applying updates is considered good practice. Auto-applying is the best you can do with the money provided. My critique here is the amount of money provided.
Also, you cannot pull a Boeing and let people die just because you cannot 100% avoid accidents. There are steps in between these two states.
you cannot pull a Boeing and let people die
You say that, but have you considered the savings?
People are temporary. Money is forever.
The real malware is the security software we made along the way.
We've known that since Norton and McAfee.
At least McAfee's antics were entertaining
The answer is obviously to require all users to change their passwords and make them stronger. 26 minimum characters; two capitals, two numbers, two special characters, cannot include '_', 'b' or the number '8', and most include Pi to the 6th place.
Great! Now when I brute force the login, I can tell my program to not waste time trying '_', 'b' and '8' and add Pi to the 6th place in every password, along with 2 capitals, 2 numbers and 2 other special characters.
Furthermore, I don't need to check passwords with less than 26 characters.
Sorry, I don’t understand. Do you mean there have to be 6 digits of Pi in there, or the sixth character must be π? I’m down either way.
We won't tell you, and the rule gets re-rolled every 14 seconds. It may stay the same or it may change.
What’s the saying about dying a hero or becoming the villain?
Maybe this is a case of hindsight being 20/20 but wouldn't they have caught this if they tried pushing the file to a test machine first?
It's not hindsight, it's common sense. It's gross negligence on CS's part 100%
I saw one rumor where they uploaded a gibberish file for some reason. In another, there was a Windows update that shipped just before they uploaded their well-tested update. The first is easy to avoid with a checksum. The second...I'm not sure...maybe only allow the installation if the windows update versions match (checksum again) :D
It's a sequence of problems that lead to this:
- The kernel driver should have parsed the update, or at a minimum it should have validated a signature, before trying to load it.
- There should not have been a mechanism to bypass Microsoft's certification.
- Microsoft should never have certified and signed a kernel driver that loads code without any kind signature verification, probably not at all.
Many people say Microsoft are not at fault here, but I believe they share the blame, they are responsible when they actually certify the kernel drivers that get shipped to customers.
A real Anakin arc right here.
Now threat actors know what EDR they are running and can craft malware to sneak past it. yay(!)
Smart threat actors use the EDR for distribution. Seems to be working very well for whoever owned Solar Winds.
SHOULD'VE USED OPENBSD LMAO
Yes but the difference is one of them is also going to help you fix it.

Programmer Humor
Welcome to Programmer Humor!
This is a place where you can post jokes, memes, humor, etc. related to programming!
For sharing awful code theres also Programming Horror.
Rules
- Keep content in english
- No advertisements
- Posts must be related to programming or programmer topics