Okay so we need to secure Michigan and Wisconsin, then break away with Minnesota and Illinois to form the Great Lakes Protectorate.
Sorry it's called the Great Lakes People's Republic. I have been irl shitposting about it too much to accept another name.
For one-to-one comms Signal is easier to get started with. Matrix requires a hosting service (or just reliance on the main matrix.org instance), or trust in a server administrator to run one. But it is good software. But unfortunately for group chat it's not as easy to get started as Discord, due to the encrypted nature of Matrix. But Discord shouldn't be considered secure or private, not really. It's just more proprietary spyware, at the end of the day.
Certainly, no matter what, no SMS.
Signal is incredibly dangerous, it's a US hosted and domiciled company, and they have a legal obligation to forward anything they know about you to the federal government if asked.
I wouldn't knock it until I learn of a situation where Signal handed data over to the government that wasn't encrypted mishmash or derived from side-channel that wasn't specifically related to Signal (the app or the protocol) itself. I do fully agree, however, that a phone number as a registration ID is bad.
But as it stands I don't consider the point that it's located in the USA to be fully incriminating. Just as I don't find it a problem that Matrix and Vector Creations were an offshoot from an Israeli tech company*. The protocol, and how it functions, are what matters.
*And yes, the major caveat here is that you can inspect and run the Matrix server code (Synapse or Dendrite), but not the Signal server code.
Read the section on NSL's (national security letters) in the link above. Any US domiciled company must give up it's data when asked, and it's illegal for them to tell their users they were forced to do so. The Obama regime admitted to issuing 60 of these every single day, there's no way Signal isn't compromised.
Matrix doesn't need to be hosted in the US, so they don't have that problem. Using any US-hosted service is a big no-no.
This is neither new information, nor something overlooked in the design of the software. Thats the point of end to end encryption and open source code: they can only give the data that they have access to, which is the sender, receiver, and timestamps, but we know they cannot decrypt messages in the middle, because it would show in the security implementation in the source code. This model prevents the carrier from knowing the contents of any messages they carry. Therefore, you have to attack one of the end point devices to get the contents, and all the warrants and secret letters in the world can't compell then to give up the content of your messages, because they do not have the means to do so.
There are legitimate problems with the security model, like its use of phone numbers as account identifiers, that render it a poor choice for doing Certain Things, but that alone does not prove it was designed as a honeypot, or that it has been secretly compromised in some way that can't be seen in the source code.
This really is worth emphasizing, because there are cases where we can reason about the kinds of exploits and vulnerabilities that do happen based on what we learn after the fact, or based on things that companies say they do or must do by implication even if they don't outright say it.
For example, I do not recommend Apple's iMessage. Why? It's an encrypted chat service, after all.
It's because when you use iCloud Backup they store the private keys. If they hold the private keys, they can decrypt the encrypted data whenever they're subpoenaed or whatever else. So if either party (you or your recipient) has this common feature enabled, your entire chat history is up for grabs. Apple themselves basically say as much here https://support.apple.com/en-gb/guide/security/sec3cac31735/web
Available-after-authentication service keys: For other services, such as Photos and iCloud Drive, the service keys are stored in iCloud Hardware Security Modules in Apple data centres, and can be accessed by some Apple services. When a user signs in to iCloud on a new device and authenticates their Apple ID, these keys can be accessed by Apple servers without further user interaction or input. For example, after signing in to iCloud.com, the user can immediately view their photos online. These service keys are available-after-authentication keys.
Didn’t Signal recently get outed as having a back door?
Honestly, as long as you're using a phone, you're at risk. As LLMs becomes more portable it's just a matter of time before our own phones will narc on us. Most of them already have some sort of ocr /image describer process happening on our photo rolls.
Can you post a source? Because I haven't heard such a thing.
There have been rumors for years but as far as I know nobody has been able to substantiate the claim. The organization that eventually produced Signal, Open Whisper Networks, received some seed funding from the Broadcasting Board of Governors (today known as the US Agency for Global Media), from which has been spun some CIA fronts like Radio Free Asia. However, this is also true of Tor, and many other non-profit private communications projects during this time, and does not itself prove any technical subversion has taken place. The source code for both the server and client are open source, and have been subject to frequent scrutiny, including full independent audits and penetration testing. No backdoor has ever been shown to exist in the code itself. Beyond that, people mostly gesture towards Moxie Marlinspike's radlib posturing and bad hair and invite people to Draw Their Own Conclusions.
No.
ffs 
stay safe out there
I disagree with the idea that people should be so overcautious as to only communicate the ideas they support or share in closed, secure, completely anonymized spaces. Generally speaking, it is my belief that overzealous Left-wing security culture does more to harm the movement in the long run than help it.
How and what you choose to communicate is a personal decision, and you should make your own threat assessment to decide what to do. It's important to protect yourself. It's also important not to so easily allow ourselves and our beliefs to be siloed off to private corners of the Internet and not expressed openly in public.
I'm a junior member of the PSL and this is their party line. Use your real name, don't hide your face, tell people exactly what you believe and who you are, if it is at all feasible for you to do so. The more people brazenly and publicly oppose the Capitalist order, the better. I don't share my real name on the Internet because I don't want groypers harassing me, but I have zero fear of fascists breaking down my door and killing me in my home. This sort of thing is exceedingly rare and, if it did happen, I would die a martyr.
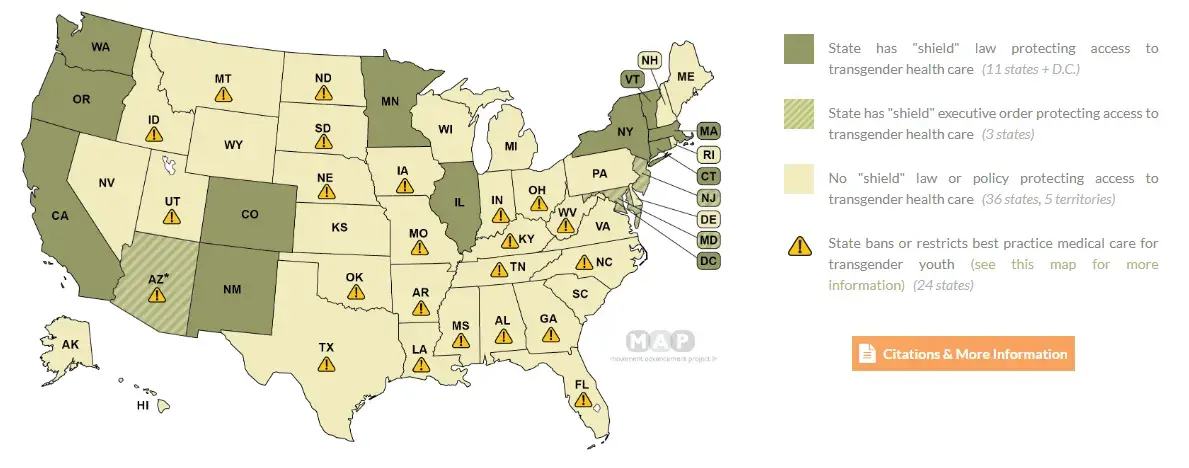
Damn, look at that one extension of green in that sea of pale yellow with warning signs in the South and Appalachia. That one safe spot that's just one train ride from Memphis, Jackson, New Orleans, Little Rock, and DFW; the spot that's just one bus ride from Nashville and then one connecting bus ride from most places in the South.
I wonder if they have a good pro-trans climate there.
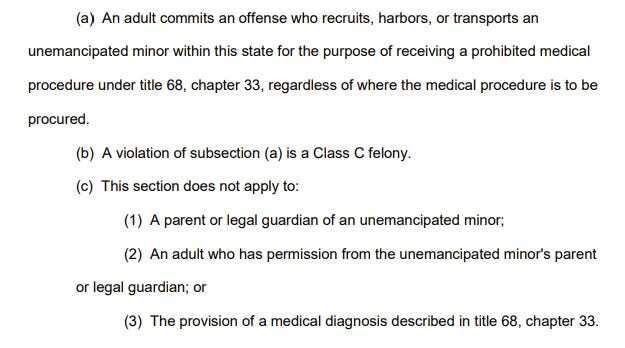
For anyone curious, here's the bill in question: https://publications.tnsosfiles.com/acts/113/pub/pc1064.pdf
Apparently they dropped it being a felony in final version of the bill, it is now a cause for civil liability to "intentionally recruit, harbor, or transport an unemancipated minor within this state for the purpose of receiving a prohibited medical procedure under this chapter, regardless of where the medical procedure is to be procured." There are exceptions cut out for common carriers, the minor's parents or guardians, and anyone designated by the minor's parents or guardians and the civil action can only be initiated by the minor's parents or guardians.
I'm curious what counts as "recruiting" kids for trans health care.
traaaaaaannnnnnnnnns
Welcome to /c/traaaaaaannnnnnnnnns, an anti-capitalist meme community for transgender and gender diverse people.
-
Please follow the Hexbear Code of Conduct
-
Selfies are not permitted for the personal safety of users.
-
No personal identifying information may be posted or commented.
-
Stay on topic (trans/gender stuff).
-
Bring a trans friend!
-
Any image post that gets 200 upvotes with "banner" or "rule 6" in the title becomes the new banner.
-
Posts about dysphoria/trauma/transphobia should be NSFW tagged for community health purposes.
-
When made outside of NSFW tagged posts, comments about dysphoria/traumatic/transphobic material should be spoiler tagged.
-
Arguing in favor of transmedicalism is unacceptable. This is an inclusive and intersectional community.
-
While this is mostly a meme community, we allow most trans related posts as we grow the trans community on the fediverse.
If you need your neopronouns added to the list, please contact the site admins.
Remember to report rulebreaking posts, don't assume someone else has already done it!
Matrix Group Chat:
Suggested Matrix Client: Cinny
https://rentry.co/tracha (Includes rules and invite link)
WEBRINGS:
🏳️⚧️ Transmasculine Pride Ring 🏳️⚧️
⬅️ Left 🏳️⚧️🏳️🌈 Be Crime Do Gay Webring 🏳️⚧️🏳️🌈 Right ➡️