this post was submitted on 19 Jul 2024
2022 points (99.1% liked)
linuxmemes
21378 readers
2174 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't fork-bomb your computer.
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
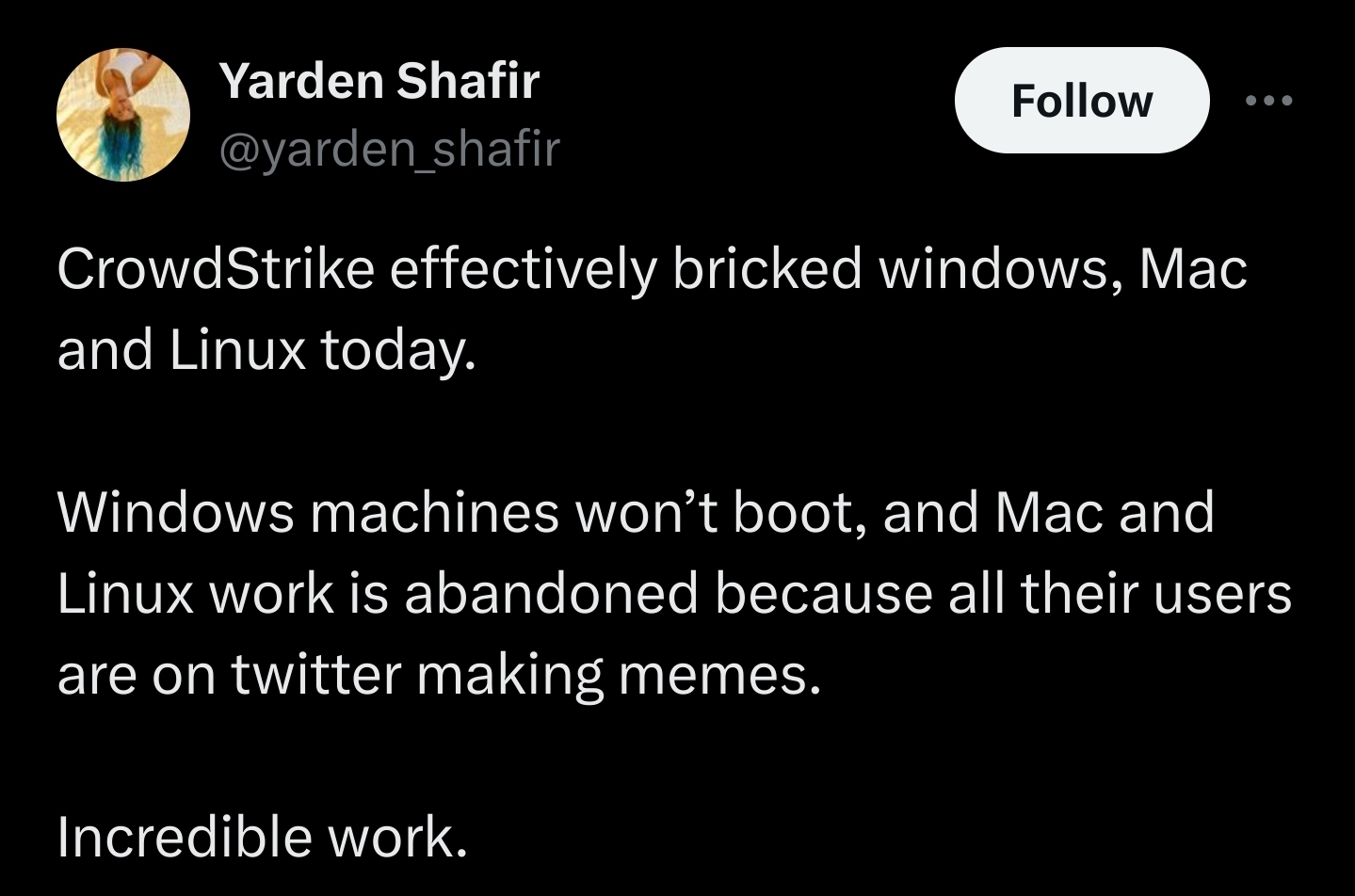
Not saying Windows isn't trash, but considering what CrowdStrike's software is, they could have bricked Mac or Linux just as hard. The CrowdStrike agent has pretty broad access to modify and block execution of system files. Nuke a few of the wrong files, and any OS is going to grind to a halt.
Probably would have been worse if this was on Linux. That's like 90% of the internet.
Good thing is the kind of people making decisions based on buzzword-bongo filled PR campaigns like Crowdstrike's are already forcing their IT to use Windows anyway.
It was a serious ask to install it from auditors that don't know what the fuck they are doing. On all ec2 machines for "reasons" I'm sure there are companies out there pushed into doing this because they don't have people willing to die on those hills.
Oddly, one of CrowdStrike's selling point is that it provides pretty good EDR for Linux and Mac. If you want crap EDR, which pushes you towards Windows, Microsoft Defender for Endpoint is the ticket.
I'm sure the three people that use Linux and Crowdstrike together would have been very upset. 🤣
Yes and no. Linux is inherently more diverse. All the different distros doing things in different ways, sometimes with different components. It's not as much of a monoculture as Windows. There isn't a Linux that 90% is.
Not only that, with Linux you can/have to manually update. Which means I hear the news before running the update
Mmm depends. I have some automatic updates on my servers: https://wiki.debian.org/UnattendedUpgrades
That's... Not great. I didn't actually think about what all these wild AV systems could do, but that's incredibly broad access.
Maybe I'm just old, but it always strikes me as odd that you'd spend so much money on that much intrusive power that on a good day slows your machines down and on a bad day this happens.
I get that Users are stupid. But maybe you shouldn't let users install anything. And maybe your machines shouldn't have access to things that can give them malware. Some times, you don't need everything connected to a network.
Always has been. I've clean Symantec A/V off way too many systems in my time, post BSOD. That crap came pre-loaded on so many systems, and then borked them. The problem is, that in order to actually protect system from malware, the A/V has to have full, kernel level access. So, when it goes sideways, it usually takes the system down. I've seen BSODs caused by just about every vendor's A/V or EDR product. Shit happens. Everyone makes mistakes, but when that mistake is in A/V or EDR, it usually means a BSOD.
It's tough. The Internet and access to networks provides some pretty good advantages to users. But, it also means users making mistakes and executing malware. And much of the malware now is targeted at user level access; so, you can't even prevent malware by denying local admin/root. Ransomware and infostealers don't need it. A/V ends up being a bit of a backstop to some of that. Sure, it mostly is a waste of resources and can break stuff when things go bad. But, it can also catch ransomware or alert network defenders to infostealers. And either of those can result in a really, really bad day. A ransomed network is a nightmare. And credentials being stolen and not known about can lead to all kinds of bad stuff. If A/V catches or alerts you to just one or two of those events and lets you take action early, it may pay for itself (even with this sort of FUBAR situation) several times over.
Fair. Thanks for that counterpoint.
When a kernel fails to boot in Linux it rollback to a previous working version so there is a chance it might recover from CrowdStrike update.
That really depends on the distro, most of them, no.