Mildly Infuriating
Home to all things "Mildly Infuriating" Not infuriating, not enraging. Mildly Infuriating. All posts should reflect that.
I want my day mildly ruined, not completely ruined. Please remember to refrain from reposting old content. If you post a post from reddit it is good practice to include a link and credit the OP. I'm not about stealing content!
It's just good to get something in this website for casual viewing whilst refreshing original content is added overtime.
Rules:
1. Be Respectful
Refrain from using harmful language pertaining to a protected characteristic: e.g. race, gender, sexuality, disability or religion.
Refrain from being argumentative when responding or commenting to posts/replies. Personal attacks are not welcome here.
...
2. No Illegal Content
Content that violates the law. Any post/comment found to be in breach of common law will be removed and given to the authorities if required.
That means: -No promoting violence/threats against any individuals
-No CSA content or Revenge Porn
-No sharing private/personal information (Doxxing)
...
3. No Spam
Posting the same post, no matter the intent is against the rules.
-If you have posted content, please refrain from re-posting said content within this community.
-Do not spam posts with intent to harass, annoy, bully, advertise, scam or harm this community.
-No posting Scams/Advertisements/Phishing Links/IP Grabbers
-No Bots, Bots will be banned from the community.
...
4. No Porn/Explicit
Content
-Do not post explicit content. Lemmy.World is not the instance for NSFW content.
-Do not post Gore or Shock Content.
...
5. No Enciting Harassment,
Brigading, Doxxing or Witch Hunts
-Do not Brigade other Communities
-No calls to action against other communities/users within Lemmy or outside of Lemmy.
-No Witch Hunts against users/communities.
-No content that harasses members within or outside of the community.
...
6. NSFW should be behind NSFW tags.
-Content that is NSFW should be behind NSFW tags.
-Content that might be distressing should be kept behind NSFW tags.
...
7. Content should match the theme of this community.
-Content should be Mildly infuriating.
-At this time we permit content that is infuriating until an infuriating community is made available.
...
8. Reposting of Reddit content is permitted, try to credit the OC.
-Please consider crediting the OC when reposting content. A name of the user or a link to the original post is sufficient.
...
...
Also check out:
Partnered Communities:
Reach out to LillianVS for inclusion on the sidebar.
All communities included on the sidebar are to be made in compliance with the instance rules.
view the rest of the comments
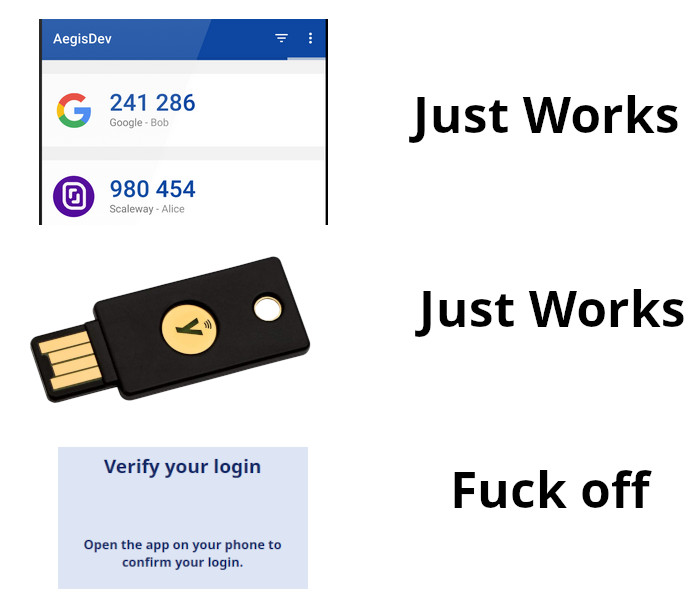
im definitely an idiot but i couldn't figure out at all how to make a yubikey work with a keepass database on android
Yubikey is only really useful for authentication with a trusted party, and not decryption. You can technically use store a secret key on it but then its two biggest advantages are gone, namely that you can't copy the key and that it doesn't use the limited storage on the device.
The yubikey can perform a hmac using a secret (supposedly) only available to the key's internals. This is used in addition to the password, so that knowledge of the password without the key, or the key without knowledge of the password, can't be used to decrypt the database. It's kind of a half second factor (I know it's not technically correct to call it that, but I hope you get the idea).
It's also in their doc (that they use challenge/response): https://keepassxc.org/docs/ and is even featured on yubico's website, which is somewhat weird but why not: https://www.yubico.com/works-with-yubikey/catalog/keepassxc/#tech-specs
The issue GP had is probably that the keepass app does not support it on Android.
What? They are super-usefully for decryption, specifically because of the inability to copy the key.
You can absolutely copy the key, because the device has to give it up to the application during decryption. Or does the application send the encrypted file to the yubikey for it to decrypt it? In which case, that's a lot better and I'm wrong.
You use a GPG key that you then add to the yubikey. The keys can only be written or deleted off the yubikey, you can't read the secret once written. Then you can use the GPG key to either encrypt a file or sign it. Check out Pretty Good Privacy and the GnuPrivacy Guard software for more information on how that works.
I use my yubikey to encrypt files, sign my work in Git, as well as the usual password authenticator stuff. You can still use FIDO, U2F and OTP codes while using the GPG too.
Check out this awesome guide on how to setup an airgapped computer to generate the GPG key. https://github.com/drduh/YubiKey-Guide
Excuse my surface knowledge on this but when setting up TOTP on Yubikey you can choose to only get an OTP on touch which would be pointless if the application had access to the secret at any point. Based on that it's probably not possible to copy it.
I believe that the decryption partially happens on the key
You're talking past each other, some Yubikeys have PGP apples for asymmetric encryption (public / private keypairs), and HMAC is a symmetric single key algorithm where the yubikey sends a resulting value to the PC/phone which is part of the key derivation inputs (even though the yubikey's root key remains secret).
HMAC is a what again?
Hash based message authentication code
This works for me on KeepassXC / Keepass2Android, and it looks like Yubico has instructions for original Keepass.
thank you, ill give it another shot
I'm a bit confused. What are you trying to get the yubikey to do?
i use keepass to store all my passwords, the database file gets synced across my devices through Dropbox, i open it with a master password, i would like to improve this by also requiring the yubikey
i am kind of confused too as to what exactly the yubikey does in this scenario. my vague understanding is that it was somehow synchronized such that the yubikey would generate sequential random 'passwords' which would be checked against the database file (generating its own sequence in the same manner).
i think it stopped working due to some desynchronization between the yubikey and the database file.
Sync shouldn't really matter, unless you're using a hotp code as opposed to a certificate or TOTP code.
TOTP being temporal, is based on UNIX time, and a seed key. A certificate will be challenged, which will require a challenge and reply all cryptographically encrypted. It's not something that's necessarily stored in some kind of sync, or rolling codes.
I'm not familiar enough with keepass to say what it's supposed to use with the yubikey in order to work. There's a few other methods that I'm sure that keepass could leverage to perform the authentication, so I'm not entirely sure what could be the problem.
okay, i appreciate you taking the time to write a response, i have no idea what you're saying though. maybe im wrong about why it didn't work.