Or just... teach them? play movie.mkv isn't rocket science.
Instructions on how to switch to HDMI 1 are currently taped to the back of my mom's TV remote
Or just... teach them? play movie.mkv isn't rocket science.
Instructions on how to switch to HDMI 1 are currently taped to the back of my mom's TV remote
tl;dr - Allegations occurred in New Zealand, plaintiff is a NZ citizen, Gaiman is a NZ permanent resident and lived there at the time. Wisconsin said "go and refile in NZ, we're only touching this case if Gaiman refuses to accept service there"
Your computer is a bunch of parts that need software to make them work. The "operating system" handles talking to the hardware directly, while the programs you run only talk to the operating system. Talking to the operating system is easy, talking to the hardware is difficult, since you may need to speak a hundred different languages to work with every possible network card, sound card, graphics card, etc.
The operating systems you have probably heard of are windows and macOS. Linux is a 3rd one.
Windows is owned by Microsoft, macOS is owned by Apple, and Linux is developed by the community and (typically) released for free. Since anyone can work on Linux, there are tons of different versions of it floating around, that are all slightly different from one another.
> want to compile 50kb C++ console app on windows
> 6 GB MSVC installation
New data tells us that mining a single Bitcoin or one BTC costs the largest public mining companies over $82,000 USD, which is nearly double the figure it did the previous quarter. Estimates for smaller organisations say you need to spend about $137,000 to get that single BTC in return. BTC is currently only valued at $94,703 USD, which seems to be a problem in the math department.
Bitcoin mining will always be profitable for the people with the cheapest electricity and largest economies of scale. There is a difficulty adjustment algorithm in the protocol that ensures this. When the price tanks people turn off thier miners, difficulty adjusts downwards, and then it takes less electricity to find a block.
tl;dr title is wrong
Literally - you can pick out English longbowman bodies from the shape of their skeletons
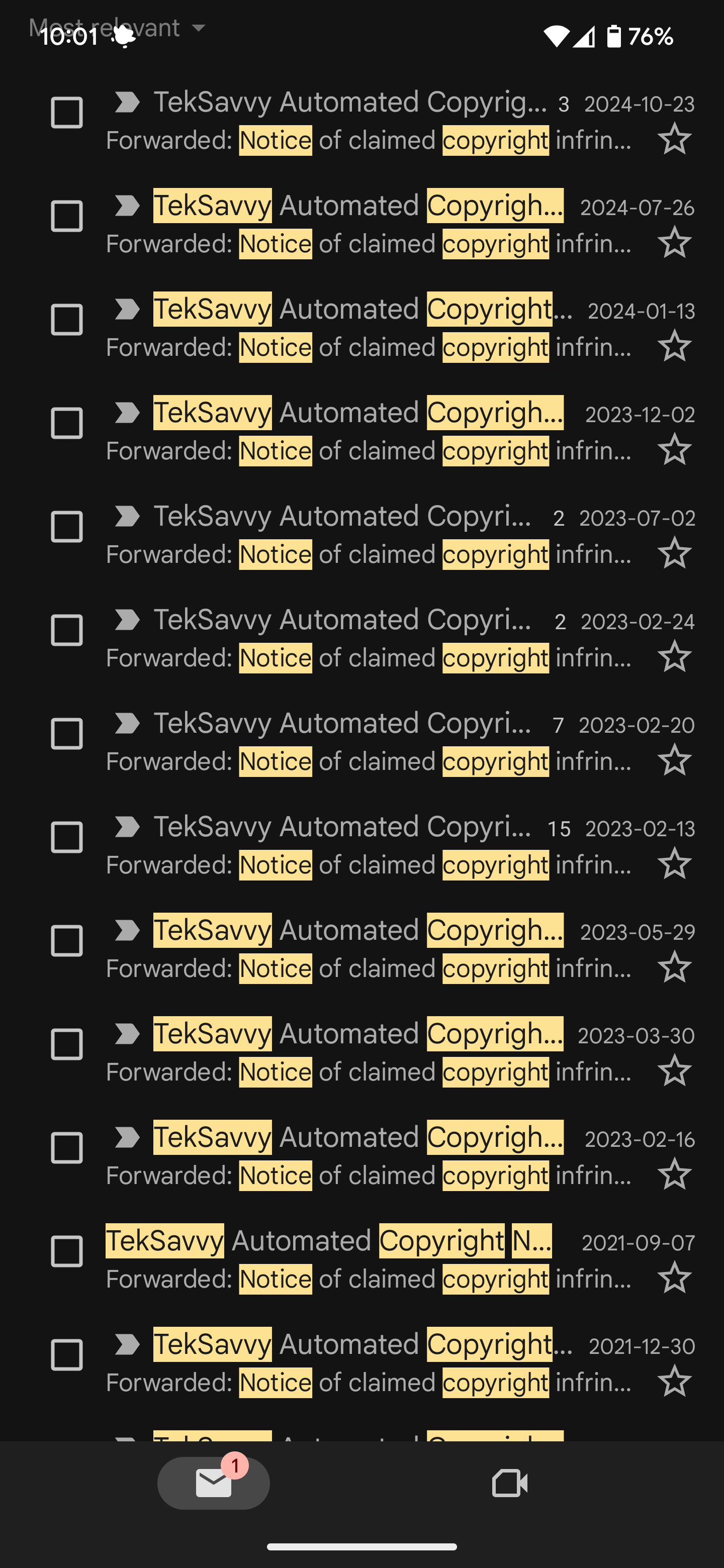
I collect these like pokemon 🙃
lol. Did this in my old building - the dryer was on an improperly rated circuit and the breaker would trip half the time, eating my money and leaving wet clothes.
It was one of the old, "insert coin, push metal chute in" types. Turns out you could bend a coat hanger and fish it through a hole in the back to engage the lever that the push-mechanism was supposed to engage. Showed everyone in the building.
The landlord came by the building a month later and asked why there was no money in the machines, I told him "we all started going to the laundromat down the street because it was cheaper"
And then when you are finally hyped that season 2 is going to be packed with surfing, they announce its cancelled
10 days without food hits differently when you are hiking through mountains 16 hours a day vs sitting on your couch
The plastic liners in and on tins and cans - referred to as lacquer in the industry - don't impact recycling. When the tins are heated to thousands of degrees for recycling, what is left of the plastic liner, the inks and UV materials; is separated and basically skimmed off, leaving the metal.
https://ekko.world/plastic-lining-on-beverage-food-cans/226751
This explanation is a really terrible explanation - it doesn't even explain the point of the study or what multiple comparisons are in statistics...
https://xkcd.com/882/
This is what the salmon study was saying - if you did a whole brain analysis with fmri without an a priori prediction you need to adopt a radically more stringent threshold for significance
The salmon in the MRI was a bowl with a million jellybeans in it